Le sigh. Another Midwest Management Summit has come and gone. These events have always been whirlwinds but this year I had ten sessions where I was speaking in some capacity. While I didn’t get to attend as many sessions as I may have liked I still came away with some really great information. To say nothing of the experiences and discussions. Point being, I won’t pretend for a second that the following highlights are truly representative of the entire event. They are just the things I personally came away with. As always, your mileage may vary.
Transformation not Migration
At last November’s Desert Edition I played devil’s advocate a bit on the whole ‘ConfigMgr is Dead’ meme that was still prevalent at the time. The product team was clearly very … very … tired of having this conversation.
This time around they decided to draw first blood. First by admitting that the whole kerfuffle is mostly a self-inflicted wound made at Ignite 2017. Second by laying down a vision for ‘transformation not migration’ which is an evolution of the ‘better together’ mantra. The focus is not how to get rid of stuff but how to adopt and integrate parts of the cloud that make sense for your organization. The goal isn’t to move all of the co-management sliders to the right; it’s to set them to what makes sense for your organization.
Most importantly, they did more than just talk. By this point most administrators are aware of the Cloud Management Gateway. Many are also aware of the beautifully simple Delivery Optimization client setting added in 1802. At MMS we saw new and arguably deeper integration with Microsoft’s cloud offerings. If you take away nothing else it’s that the product team has a program manager dedicated to ‘build[ing] data analytics solutions to help customers move to latest Windows & Office’: Deepam Dubey. This is his life now. Send him drinks.
Technical Preview 1902.2 introduced integration with Office Analytics and then Technical Preview 1904 gave us a new Office 365 ProPlus Upgrade Readiness node in the console. If you’re not familiar with the readiness tool it was created to help organizations identify plugins or VBA macros that are blockers for Office 365 adoption. Using the powerful mix of asset intelligence and the scale of global telemetry you can quickly identify devices that are quick wins and devices that are likely to need remediation. Most importantly, you can do this before you even attempt to migrate them.
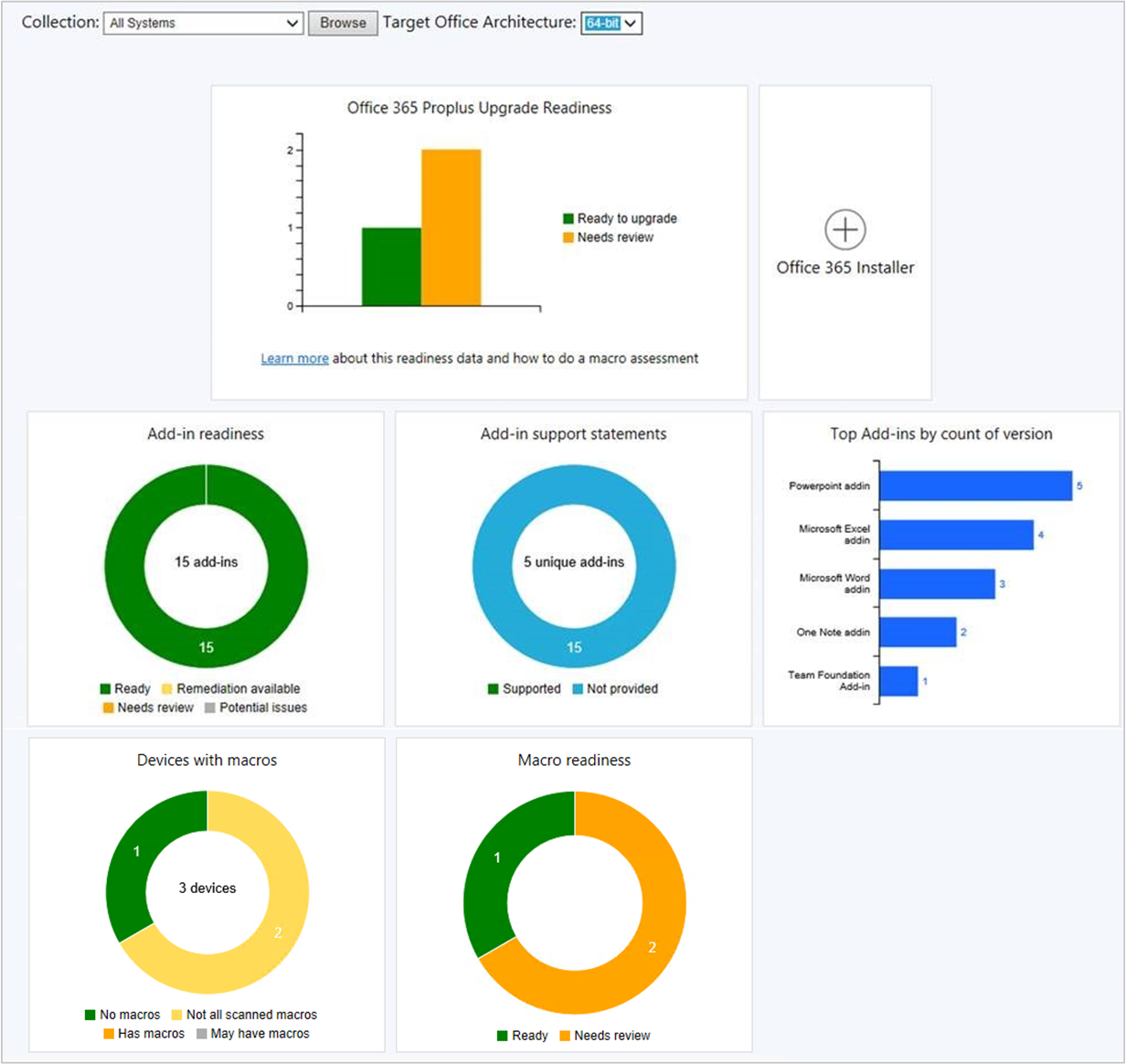
With a dedicated PM for this kind of stuff I think it’s safe to say that these integrations aren’t the last we’re going to see. I’d love to see Upgrade Readiness get integrated to help with Win 10 in-place upgrades. Imagine getting a list of applications and devices in your environment that have known issues with the next version of Windows 10 before you push it out to the first device. Then, being able to immediately put that information to work within the ConfigMgr console. If servicing is to ever take over the world this is the kind of stuff that’ll help make it happen.
MBAM: I’m Not Dead!
One of the questions I came to MMS with was the future of MBAM. In July of this year MBAM 2.5 SP1 goes into extended support and Microsoft had stated clearly that it would be the last version of MBAM. I heard rumors about the product team taking on this challenge and wanted to get some direct confirmation. They beat me to the punch and announced that MBAM functionality will be directly implemented into both Intune and ConfigMgr. During the state of the union address we saw an actual MBAM node in the console. If I had to guess this will be iterative instead of big-bang. A true migration path will eventually exist but not from the start. For now, just know that MBAM has a path forward and that you can sit tight and wait for that path to unfold.
User Experience: Settle Down there People
In Current Branch 1902 the team added in an option to replace the software update reboot notification with a true dialog box. For users with multiple monitors, especially when one of them is a laptop monitor, having a small pop-up outside of their periphery vision wasn’t really cutting it.
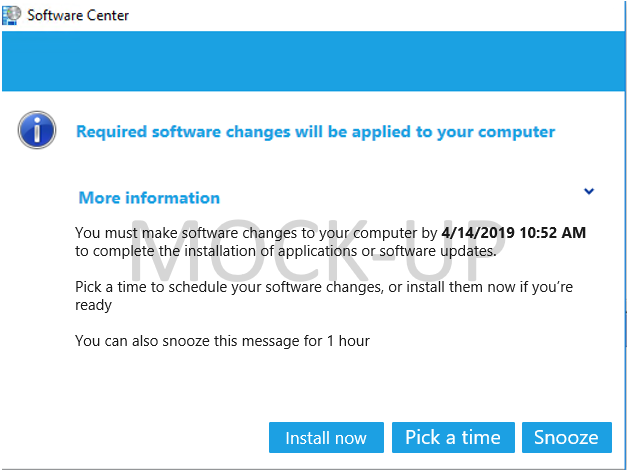
While the new dialog was a great step forward I was hoping to clarify that it was only a first step. I can appreciate why administrators and thus the product team focused on the reboot notification that users hate seeing. However, I feel there’s a better way to attack it. I want users acting ahead of the deadline and scheduling the installation and reboot when it’s convenient for them. It’s 2019 for crying out loud … most people aren’t surprised that updating is a thing. Unfortunately, the current implementation makes it very unlikely if not practically impossible to engage your users pre-deadline.
A conversation on Twitter turned into a last-minute lunch session. I wasn’t expecting anyone to show up and figured we’d have a small round-table of nerds just spit-balling. I was dead wrong as usual. We crammed 60+ people into a small room and Avi Prasad brought his A-game having stayed up late the night before to pound out a slide deck. I took away three key things from this session:
- User Experience is a current focus for Avi and the team.
- Administrators are passionate about the user experience.
- None of them can agree on a single solution.
It was a lively session with all sorts of ideas bandied about. Imagine a room full of admins shouting out ideas a mile-a-minute. There were moments where you couldn’t track what was going on, people were that worked up about it. Avi and team have their work cut out for them to come up with some meaningful middle ground that can’t possibly please everyone but still drives the product forward. For my money the UI that Avi mocked up is about as good as can be expected and would be a great first try. To clarify, the below is purely just that: a mock-up. I don’t care though … ship it!
Security: MFA All The Things
I’m not quite sure I’d go so far as to call this a theme this year but a two-parter I really wish I hadn’t missed was Tom Degreef and Kim Oppalfens session on securing ConfigMgr. I heard a few people talking about it and just dug through the slide deck. Hopefully those guys blog the information in more detail but among many … many … other things they confirmed my dislike for Client Push. If you haven’t heard about PowerSCCM (I hadn’t) then I highly recommend you put it on your to-read list this week.
Related, if your organization has adopted Windows Hello for Business then with the release of CB 1810 you can now require WHfB for console access. Which is to say that you can require multi-factor authentication for ConfigMgr. Seriously … go do this. Right now. Between years of ‘Using ConfigMgr for Evil’ sessions, what Tom and Kim showed, adding in Bitlocker recovery keys (MBAM), and the ability to do MFA in ConfigMgr this is a no-brainer take-away from MMS this year.
WSUS: I Wish I Knew How to Quit You
At this point I’m just going to keep going to MMS and asking what the plan is for dealing with WSUS. Each time I’m hoping beyond hope to hear ‘we own it’ or ‘we will rebuild’. At MMS 2019 the story was mostly the same on that front: there is a PM for WSUS on the server OS team and the ConfigMgr product team thinks the OS team is finally realizing the problem they have and the urgency in solving it. I remain skeptically optimistic.
That being said, the product team hasn’t just sat around accepting their fate either. In Current Branch 1810 they started declining superseded updates in WSUS as well as running maintenance on downstream sites. In Technical Preview 1904 they added the option to add indexes that drastically improve the WSUS Cleanup Wizard performance. Kudos to Steve Thompson and Benjamin Reynolds for finding those.
What’s really telling though is that the maintenance options have been added to their own tab in the site’s Software Update Point component settings window. There’s a huge amount of dead-space below the two current settings and the plan is to fill that up. My first recommendation would be to include the ‘Remove unused updates and update revisions’ cleanup wizard option when ran by ConfigMgr. Add in a ‘block all synchronization’ option so that maintenance could be done in parallel without fear and then we’d really have something.
I can’t end this section without calling out Rae Goodhart who is the lead developer for software updates in ConfigMgr. In the brief time we were able to talk over the week she taught me several things I hadn’t known about software updates. She was also kind enough to attend Daniel Ratliff and I’s session on getting WSUS under control and fact-check us live. If you’re going to be called out for being wrong make sure you’re on stage, in front of a hundred or so people, by someone who knows way more than you do. It’s the only way to fail and I consider myself a connoisseur of failure.
Finally, the End
That about wraps it up for me. Again, I fully expect that other attendees have different takeaways. Totally cool, let us know what they were.
I unabashedly love this event and apparently was so blatant about it they felt the need to bribe me with a set of noise-cancelling headphones to shut up or something. I’d like to give a shout-out to the whole MMS team who puts this thing on. Sure, everyone wants to give Brian Mason a pat on the back. Heck, he almost deserves it. That and it’s funny to see if you can pat him hard enough to send his hoverboard flying. It takes a dedicated team that sometimes does thankless work like answer emails from me to put on something this successful. My onsie’s hoodie off to them.
If you missed out then start planning for MMS Jazz Edition in November which still has tickets available.
If you’re not on Twitter stop being stupid and get on Twitter. You don’t even have to tweet. Just follow David James, a few of the MVPs, and the product team that I copiously linked to above. Sure as heck don’t follow me. If anyone says anything half-way intelligent someone above will like or retweet it. To ignore Twitter is to miss out on the best news stream for ConfigMgr. Even if your organization blocks it you can spend 5 minutes a day on your phone or at home to keep up.

Great write up Bryan.. glad to know that you liked our features from MMS’19..
Sure did. Now get crackin on Upgrade Readines. 8)
Bryan, thanks for the recap for those of us that could not attend. I really enjoy reading your Blog and appreciate your contributions on Reddit and the various community sites. I was able to get approval for MMS Jazz edition and grabbed my tickets already, cant wait to get to meet a few of the guys from Reddit, Twitter etc..
WOOT! Glad to hear that you’ll be joining us. Be sure to say hello. I’ll be there either as a speaker or representing my employer (Recast) who _just_ signed on as a sponsor.